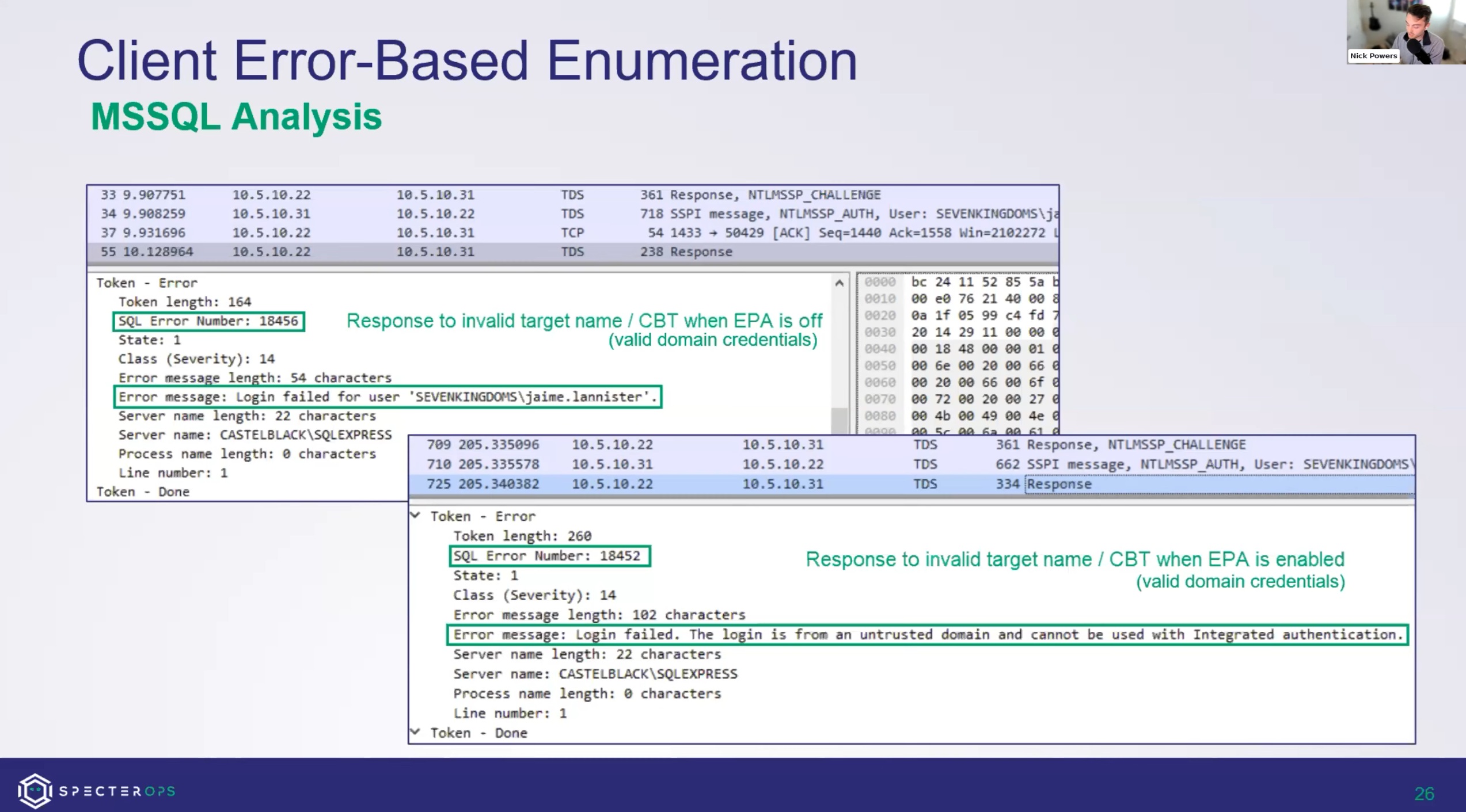
Less Praying More Relaying - Enumerating EPA Enforcement for MSSQL and HTTPS
It's important to know if your NTLM relay will be prevented by integrity protections such as EPA, before setting up for and attempting the attack. In this post, we share how to solve this problem for additional protocols (MSSQL and HTTP), as well as publish RelayInformer tools to automate the solution.